JS Business Solutions Blog
One of the greatest challenges for businesses is how they protect themselves from threats, including both the physical and digital spaces. Worse yet, the responsibility falls on more than just your IT department. Every employee needs to know and understand how their actions impact operational continuity and business success.
Today’s businesses need an established cybersecurity strategy. It’s as simple as that.
However, many businesses need guidance to create this strategy, which is why the National Institute of Standards and Technology has developed a framework for proper cybersecurity protection. Let’s walk through this framework and discuss what you need to do to meet its requirements.
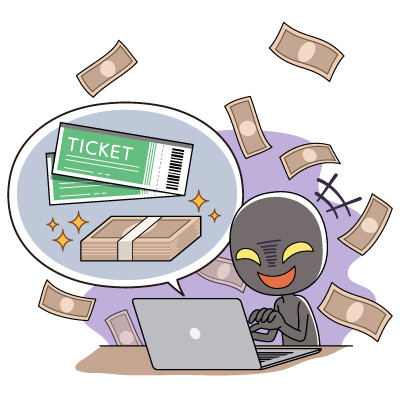
Problems with cybersecurity can really sink your business. Unfortunately, more opportunists are out there today looking to profit off of business’ lack of vigilance. One example of this are large-scale scam operations that have been running in Southeast Asia, and they are now spreading to other parts of the world. These scams, called "pig butchering" scams, have caused major harm, with around $75 billion lost worldwide in 2023.
Sextortion scams are far from glamorous. These attacks involve a scammer claiming to have compromising photos or videos of their target engaged in explicit activities—often suggesting this footage was captured through their online behavior. The scammer then threatens to release this material unless a ransom is paid.
In this blog and our conversations with clients, we frequently discuss the importance of protecting accounts with complex and unique passwords and multi-factor authentication. These actions are crucial, but there is a tool out there that can really improve any business’ account security: the password manager.
Today, we’ll discuss the password manager and why it is such a great tool for keeping passwords complex and secure.
Cybersecurity tops the list for any business’ needs, particularly when one considers just how many threats are out there today. This makes it essential that today’s businesses (yours included) put an assortment of cybersecurity tools and protections in place.
We’ve assembled a list of the ones we recommend.
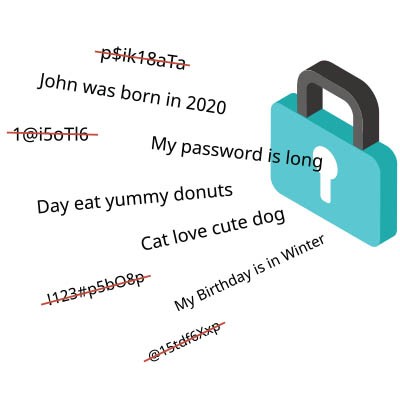
Strong passwords are extremely important these days. Cybercriminals only need low-end hardware to crack millions of passwords at once, so it's critical to use random, complex strings of characters.
The bigger problem most users have is using unique passwords for each and every account. Any account is liable to be compromised at any given time, and you might not even know about it. If your password is compromised, the bad guys can use it to access all of your other accounts.
Sometimes, it seems like the most complex aspect of modern technology is the naming conventions used by big vendors for all of their products. It’s a problem with consumer electronics, it’s a problem with enterprise products, and sometimes it feels like some companies make their products as confusing as possible on purpose… I’m looking at you, Microsoft.
When it comes to protecting your PC from viruses and malware, there should be zero confusion. Hopefully after this article you’ll have the confidence to make the right choice for your business.
Cybersecurity is necessary for businesses to function, but when it turns to overreaching and overinvestment—a concept called cybersecurity sprawl—it becomes a problem. Today, we want to highlight some of the many challenges that can come about from cybersecurity sprawl, as well as how you can avoid it.
You’ve more likely than not purchased a ticket through Ticketmaster at some point in your lifetime, so you might be interested to find out that Live Nation Entertainment—Ticketmaster’s parent company—has had to file an 8-K with the Security and Exchange Commission to admit that 1.3 terabytes of data had been hacked. The result is that more than 560 million customers’ personal information was stolen from company servers.
Asset management security has become a critical concern for businesses. It's not just about protecting physical assets anymore. More assets than ever need to be safeguarded, but securing these assets is not straightforward. It involves a complex interplay of strategies, from attack surface management to cybersecurity compliance.
Let's explore some key considerations when securing your asset management processes.
In today's digital landscape, data breaches and privacy concerns are more prevalent than ever. Your team needs to protect important information by following data privacy practices, which also helps boost your company's reputation. It needs to be a part of your company culture.
Here are effective strategies to encourage a culture of data security within your team.
Password management is always a sticking point for businesses (and even individuals), but it doesn’t have to be as hard as you make it. With the increased risk of cybersecurity attacks and advanced threats, you cannot rely on one singular password as you may have once done. Instead, you need complex passwords housed in a password manager that makes remembering your passwords significantly easier.
Personally identifiable information—or PII—is critically important data for individuals and businesses, not only because operations rely on many of these data points but there are also significant circumstances for losing it. Of course, to properly protect PII, you need to know what the umbrella term of PII includes.