It’s hard to tell people that “we are under attack” all the time and actually mean it. There are a couple of reasons for this. First, the more you tell people they are under threats that don’t actually affect them, the more distrust or even disdain develops for the issuer of these revelations. Second, people will never actually understand that they are under threat until something happens that proves to them that they need to be more careful.
JS Business Solutions Blog
With the threat landscape littered with companies that don’t take their IT security seriously, it's hardly surprising that many are embracing what's known as a zero-trust policy to fortify their security measures. What exactly does zero-trust entail, and why does it prove so formidable in thwarting potential risks for your enterprise? Let's delve into this topic in today's blog post.
Concerns over operational expenses, particularly regarding technology, weigh heavily on many business owners. For some, these expenses can spiral out of control, leading to financial problems in vital areas of the organization. Every business needs to ask how it can rectify its IT spending to bring on a culture of overall improvement.
One of the most dangerous types of threats is the many phishing scams you and your employees could fall victim to. While it might be tempting to poke fun at the people who succumb to seemingly obvious phishing attacks, the reality of the matter is that some phishing attacks are anything but, and they are only growing more sophisticated over time.
When it comes to network security, there are many common suggestions from IT professionals, like utilizing robust firewalls and antivirus measures. However, it’s easy to overlook some of these practices, especially if you are not necessarily a trained IT technician. We’re here to provide a short guide to three of the most common security pitfalls organizations like yours will likely face during normal everyday operations.
One of the most effective ways to reduce cyber risks is through comprehensive employee cybersecurity training. You protect your organization by ensuring that your workforce has the knowledge and skills needed to identify and thwart potential threats. Here are five essential considerations for implementing successful employee cybersecurity training programs.
With so many new and emerging threats to worry about in today’s cybersecurity landscape, it’s no wonder that some businesses and employees might be operating from a knowledge deficit regarding network security. We’re here to change that with a quick overview of the three biggest overarching threats your business must face and prepare for.
You might wonder how your business can possibly stand up to the countless cybersecurity threats out there, as even with training for your employees, it seems likely that something bad will happen eventually. This defeatist attitude isn’t necessarily productive, and it’s actually one that your team might embody if you don’t frame your training in the right way. Let’s look at some ways you should not bring up cybersecurity training and why you might be inadvertently sinking your successes.
Data security is an ongoing challenge, given the evolving tactics of hackers and scammers. IT administrators face a complex situation as these threats become more sophisticated. Employing security measures such as multi-factor authentication (MFA) or two-factor authentication (2FA) has emerged as an effective means to enhance organizational data protection. In this discussion, we will go into the advantages of this approach while acknowledging its limitations in providing comprehensive security.
We know that living in a constant state of fear of being scammed is not ideal, but it’s the unfortunate reality of living in today’s technologically advanced world. The good news is that it’s never too late to learn how to avoid them! Let’s discuss how you can be more aware of the challenges of scams not only in a business setting, but in everyday life.
We’re always telling people to avoid clicking on suspicious links, but the bad guys are making it harder to tell the difference between a legitimate URL and a suspicious one. We’re going to try to simplify it for you, and have you focus on the placement of a single punctuation mark in a link to tell if it might be safe or dangerous.
Against all odds, remote work has been gradually accepted, but regardless of how your organization does it, it would be imprudent to overlook the obvious cybersecurity risks presented by remote work. Let’s take a look at the essence of zero-trust security and explore why it has evolved into the standard that organizations of all sizes should adhere to.
With the holiday season upon us and online shopping surging, instances of scams targeting the popular e-commerce platform Amazon have become increasingly common. The majority of these scams involve impersonation tactics, posing a significant threat to unsuspecting users. With the festive season underway, it's crucial to be aware of the types of Amazon scams prevalent and take measures to avoid falling victim to them.
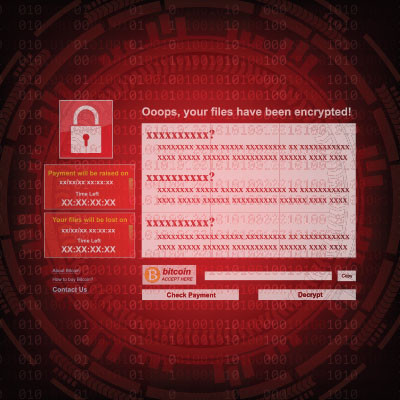
Ransomware is a real problem; I mean, a real problem. Not only does it create serious problems for any organization that is victimized by it, it is about to be a completely pervasive problem for everyone. It is extremely important for your organization to take the threat of ransomware seriously by implementing a strategy to keep it from being an issue. Today, we offer a three-pronged approach to doing just that.
It’s easy to think of email as something that just works. You open up Outlook or log into Gmail and your mail is there. Most people aren’t even aware of the vast, complex set of systems required for email to even work—and we don’t blame you. It’s extremely complicated.
That being said, if nobody is actively managing your email, providing protection for the underlying technology, and making sure that it was and remains configured properly, it’s possible that your email could be working fine while opening you up for unseen threats.