JS Business Solutions Blog
If you’ve ever used Google Lens on a mobile device, you know it’s a pretty impressive little tool for contextual searches. However, you can also use these capabilities in the Chrome browser., searching for anything visible in the browser—from text to images, even one captured from a video.
Let’s go over how.
Are you finding that some of your younger hires aren’t sticking around nearly as long as you’d prefer them to? There’s a good chance that these employees are experiencing a relatively recent phenomenon called “shift shock,” the latest workplace trend focusing on employee engagement and satisfaction. Let’s examine shift shock and how to avoid its impacts in your business.
In business, email is one of the tried and true methods of communication. Unfortunately, there are many out there searching to breach a network, whether it be to deploy malware or lie in wait until they have access and cause havoc from within. Regardless of what strategy hackers and scammers use, it is important that users understand what to do to protect themselves and their organizations’ email. Here are some tips to keep in mind.
When you’re using the Internet, how often do you find yourself using so many bookmarks that the bar simply cannot display what you want it to? You can make things a bit easier by saving some space on your bookmark or favorite bar by only showing the sites’ favicons. Don’t know what a favicon is? We’ll cover that too!
If we asked you to identify the one hour of your day when you get the most done, would you be able to tell us? Even more interestingly, do you know how to get the most out of your so-called “power hour?” Let’s take a look at some of the theories about how you can make the most out of your most productive time in the workplace.
Have you ever thought about password protecting a zipped folder so that only authorized individuals and users can access it? While Windows might not have built-in functionality for this type of protection, a free app called 7-Zip gives you the power to do so. Let’s go over how you can use 7-Zip to password protect a ZIP file on your Windows PC.
Sometimes you will find something on the Internet and think, “Wow, I’d love to save this, but I also love PDFs.” Well, for instances like this, there are features built into your web browser that allow you to do just that! Let’s go over how you can save a web page or image as a PDF directly from your browser.
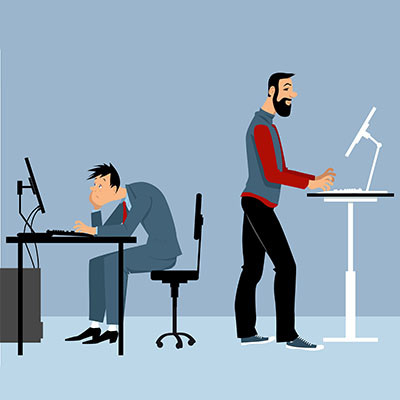
Standing desks have become quite popular, especially as people grow more health-conscious post-pandemic. These desks are a little on the pricey side, so you might be wondering if they are really worth the investment. Can the benefits make implementation worthwhile for standing desks? The answer might surprise you.
Have you ever thought about protecting a specific file or folder on your computer? You could always hide the file, but this isn’t doing much to protect it from anyone who has access to your computer and its settings. Sometimes it takes a stronger approach. Windows has some basic file encryption functionality built into it, so let’s go over how you can use it to protect a specific file or folder on your computer!
Is your desktop littered with random files or folders that need to be organized? Do you have a handful of folders that you absolutely need but would prefer if they weren’t out in the open all the time? Windows has built-in functionality that lets you hide certain folders from view, if you want, and it’s a great way to clean up your desktop. Let’s get into how you can hide these folders from your desktop or Documents view.
Managing your email can be challenging, especially if you are a business owner. We’re sure you get countless emails on a day-to-day basis, and it can be difficult to assign them priority or triage them accordingly. All of this leads to one messy inbox that can get in the way when you need simplicity most. How can you make sure your inbox’s organization is not holding you back from achieving maximum productivity?
Getting the right technology for your business can be confusing and downright frustrating if you don’t know what you are looking for. After all, technology is supposed to make life easier and keep your business more efficient and organized. With so many rapidly evolving technologies now available, it can be hard to choose which to deploy inside your business. Today, we’ll go through three tips that can help you identify and deploy the technology that will work for you.
The modern computer is a marvel, but they can be quite the investment. It stands to reason that when you purchase new hardware—whether it be for yourself or your business—that you should want it to last as long as possible. For this week’s tip, we wanted to go through five things you can do to protect your computer from wear and tear.
Chances are that, if you are a user of an Android device, you prefer Google Chrome as your mobile web browser. However, did you know that you can change your default web browser to a different one? All you have to do is know which browsers are available to use; then all it takes is a quick settings adjustment!
News flash, cybersecurity is pretty important, and the Internet is chock-full of threats that you need to take seriously. However, with today’s youth practically growing up connected to the Internet, it becomes even more important than ever to ensure that they are aware of cybersecurity best practices early in their lives. To this end, Google has created a platform called the Be Internet Awesome initiative.
Staring at a bright computer screen all day can bother your eyes, especially if it’s done on a routine basis. We know that staying away from computers and devices is something that we cannot really get away from in the business environment, but you can take steps to make it more manageable and easier on your eyes through the use of Dark Mode.